Satisfy a Variety of
Out of the Box and Custom Needs
These connectors are part of our IIQ Common toolkit
Options Available
The Loopback Connector connects IdentityIQ to itself, allowing you to manage a variety of common IIQ features as though they are entitlements. For example, you can enable or disable an Active Directory account simply by adding or removing a Loopback account attribute.
What’s important about entitlements? They can be added and removed automatically by roles! While IdentityIQ allows you to create accounts with roles, the product doesn’t support disabling or deleting accounts the same way. With the Loopback Connector, you can!
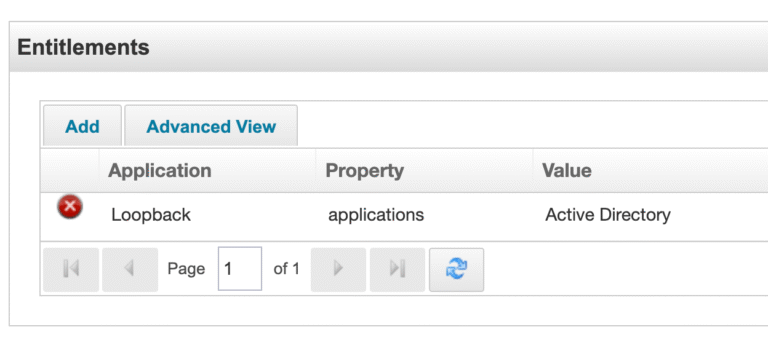
Using XML configuration on the Loopback Application, you can specify what happens to the Active Directory account (for example), when the entitlement is lost. Should it be disabled? Deleted? Have all of its entitlements revoked and then deleted? You can do all of this and more!
Loopback can also manage capabilities and workgroups as entitlements.
For maximum flexibility, you can also create entitlements that simply run arbitrary Beanshell scripts on “add” and “remove”. Role-based automations that can do literally anything? You got it with our Loopback connector!
Of course, the connector supports the usual IIQ connector functions: partitions, incremental aggregations, and more.
Have you ever run into a system where provisioning is done via a simple web service call, but aggregation requires a database query? Or a semi-detached connector, where you can provision automatically but only get confirmation of provisioning in a weekly flat file?
The dual delegating connector creates a wrapper around two IIQ connectors: one used for “write” operations and one used for “read” operations. The connectors need to share Schema attributes, but are otherwise unrelated.
We offer “command connectors” implementing command flows on a local shell, via telnet, via SSH, or via Powershell. Commands can be Velocity templates (like IIQ’s email templates), allowing you to dynamically populate values as needed. Commands can be expect scripts, allowing provisioning to interactive shells. SSH command connectors can invoke commands via “jump servers”, allowing a layer of indirection between IIQ and the target system.
There is very little that’s beyond the command connector framework.
Snowflake’s JDBC driver prefers that you authenticate using a pre-shared key pair.
IIQ’s JDBC connector doesn’t support key pair properties.
Our extension of the JDBC connector can easily support key pairs.
Snowflake and IIQ: together at last.
Files delivered via ETL processes often have daily filenames.
You’ve seen them before. Something like this: users_feed_20250701.txt.
IIQ’s DelimitedFile connector can’t handle a variable filename. Our custom extension of the DelimitedFile connector is otherwise identical (it really is a Java class extension), but allows you to dynamically calculate the filename before aggregations.
Where to find this library:
The repository containing the open source portion of the IIQCommon framework can be accessed via the button below. You can request custom features for this library or get more information by contacting Instrumental Identity using our Contact form!